Getting access to any remote machine has become a great necessity over the course of time. You can make a connection by using a remote machine in various ways. But, it also depends a lot on the kind of OS you are using. This can be done using a protocol called Secure Shell (SSH). Find out more about it!
What Exactly Is SSH (Secure Socket Shell)?
With the help of an ssh command, you can establish a stable connection between a server and a PC. So, in simple words, SSH is a protocol that allows a connection. Using this protocol, users can type commands and manipulate the server.
This protocol is mainly used by administrators of systems and network servers or anybody who is in charge of managing remote machines from a computer with high-end security.
How Does Secure Socket Shell Work?
To make a thorough connection, you need to have a client-server and a corresponding server. All you need to do is install the SSH client so that you can make the connection to a remoter machine or even a server.
To start the connection, the client uses the information of the host, and upon verifying, if the information is correct, then a connection with encryption is generated.
After the connection is made successful, a component known as SSH daemon, responds to client connections and then both of them would be exchanging the data of identification. Then, verification starts. After the verification of the information is correct is done, a new session is created.
How To Connect To A Remote Server Using SSH?
In order to know how to use ssh to a remote server or machine, you need to do a few things that are mentioned below:
Install OpenSSH Client (For Linux OS)
If you have a Linux OS, then you need to install OpenSSH Client which is available online. However, first make sure that whether it is already installed in the OS or not because oftentimes it already stays installed in the system.
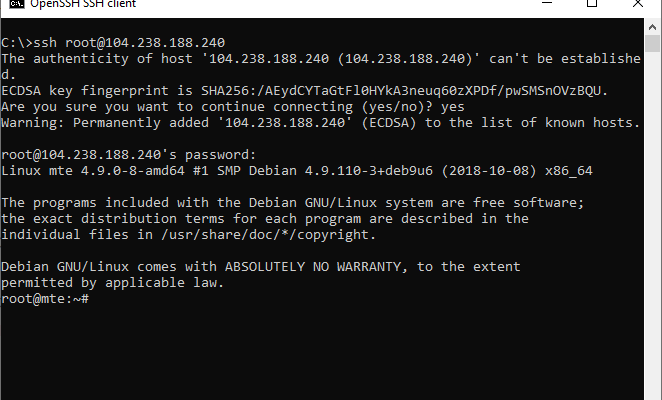
Once you’ve installed the application, you need to connect to your server. Launch the SSH terminal and then write the ssh linux command, “ssh your_username@host_ip_address” and then hit the “Enter” button.
Then write your password and then again hit the “Enter” button. After this, you may be asked whether you want the connection to continue or not. Write “yes” and then press the “Enter’ button.
After this, a fingerprint key named ECDSA key will be added when you get connected to a server that is remote.
Keep in mind that it is advisable to use a private IP address instead of a public address when you are connecting through the same network. Also, make sure that the TCP port number is 22 as that is the default number.
Things To Keep In Mind While Connecting To A Server Using OpenSSH
If you are unable to make a connection, check these things:
Make sure that the remote machine’s IP address is correct.
The port of SSH is not incorrect or blocked by a firewall.
The credentials are not incorrect.
The OpenSSH software downloaded, is installed correctly or not.
Install PuTTY Software (For Windows)
PuTTY is free software available on the internet, which is an open-source platform of SSH.
First, download PuTTY software from the web and then install it on the PC.
Launch the application by clicking on it. Once the configuration box appears on the screen, type in the IP address or the hostname and put “22” in the TCP Port section. If you have a different port where the server is running, use that port’s number.
In the “Saved Session” section, select “Linode” then click on the “Open” option at the bottom.
If you are using PuTTy for the first time then you will get a prompt alert on the screen saying that the fingerprint of SSH key is new and that whether you want o proceed with that or not.
Do not select anything. Instead, sign in to the “Linode” by using “Lish” and then type the command “ssh-keygen -E md5 -lf /etc/ssh/ssh_host-ed25519_key.pub”
You will be given an output that will be a combination of letters and numerics. Match the output with what PuTTY is showing in the prompt box. This is the fingerprint. It should match with what PuTTY is showing. If yes, then proceed and then connect to Linode.
Keep in mind that if the fingerprints are not matching, then restrict yourself from connecting to the server. You will not be given any warnings further. However, if you do receive a warning when you already have the host key then you may not have a secure connection.
In such a case, it is highly advisable to not go forth with the connection and understand further.
SSH Tunneling
You can use SSH tunneling to get a more secure connection as it provides a secure channel when a connection is establishing. To get this, do the following:
Go to the configuration box of PuTTY and then select the option called “Connection”. Then, visit the “SSH” and then select “Tunnels”.
Select the “Source Port” option and type 3306” in it. Then type “127.0.0.1:3306” in the field of “Destination”. Then click on the “Add” option and select “Open”.
After the connection has been made successfully, you will be taken to the “MySQL” local ssh server, which is encrypted with SSH. After this, you can get access to any database without any hassle.